How to Automate Supply Chain Risk Reports: A Guide for Developers
Do you use Python? If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API.

Since the onset of the war Palestinian terrorist group Hamas launched against Israel on October 7, our cyber team has been monitoring the deep and dark web, including alternative social media platforms, to gain more insights into the hidden realms of the ongoing war.
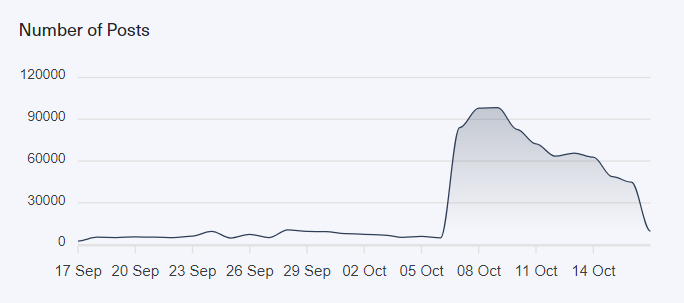
Before we even took a closer look at those spaces, we could instantly see a huge spike in the number of daily average posts, comments, or text messages containing keywords related to Israel, Hamas, or Palestine on these networks.
In the next image, you can see that the number surged from around 5,000 daily mentions to an astonishing 100,000 mentions in the first week of the war.
Our dedicated cyber team conducted an analysis of the relevant illegal and adverse content we crawled and sorted them into different types.
There has been a wide use of various online platforms to spread shocking and disturbing content by Hamas and their supporters to generate fear and intimidation among Israelis and supporters.
In the days after the war started, we have seen an unprecedented surge in the use of Telegram to spread such obscene content. As we covered in a previous Dark Web Pulse article, Telegram is widely used by radical and terrorist groups like ISIS or Neo-Nazi groups. This time, Hamas and the Palestinian Islamic Jihad, as well as their supporters, have turned to Telegram to spread shocking and disturbing videos and images, featuring injured, dead, and abducted Israelis in Gaza.
This deliberate use of disturbing images on Telegram has intensified the psychological warfare associated with the conflict. The exclusive release of such content has drawn a lot of attention from people who are eager to stay informed, particularly when government bodies have been slow to provide answers regarding the status of abductees and missing persons.
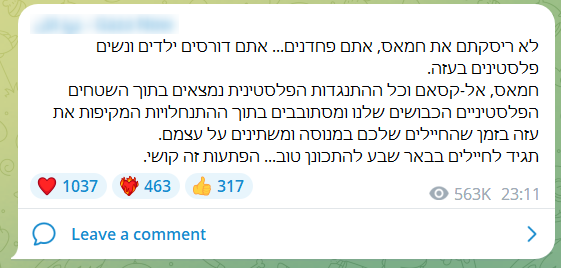
However, it’s not just Telegram but we can see this type of content on alternative social media too.
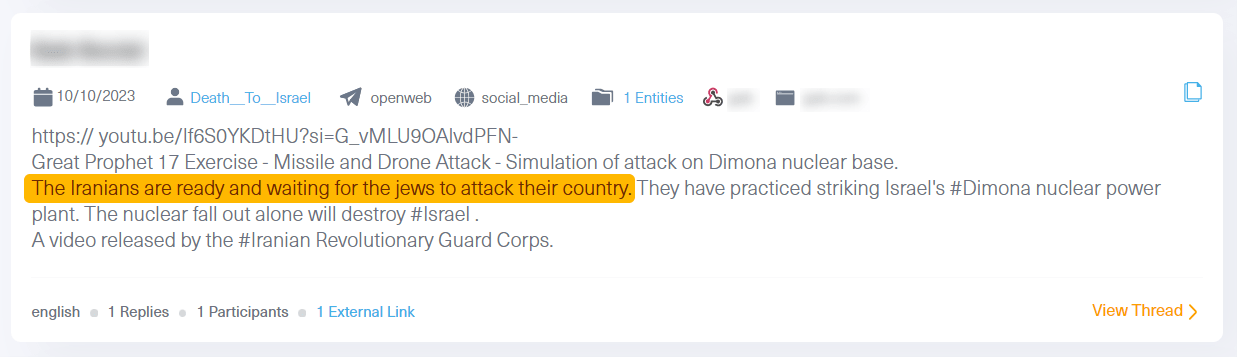
The following post was written by a newly created user “Death to Israel” on a known alternative social media platform. This user who seems to be promoting Iranian agendas aims to cause anxiety among the Israeli public.
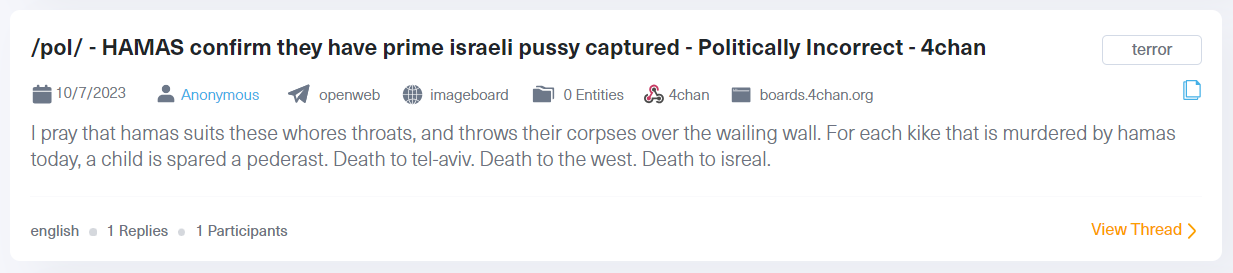
The most notable uptick was observed in the number of radical discussions concerning the war between Israel and Hamas. These types of conversations have been primarily happening on alternative social media networks, imageboards, and exclusive open web forums affiliated with extremist political groups. These discussions include hate speech, incitement to violence, explicit calls for violence, and endorsements of terrorism.
These platforms are also used to spread misinformation and fake news on a large scale.
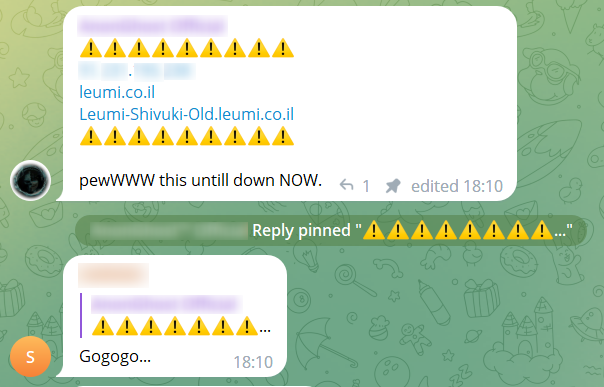
The cyber space has been used by Islamic hacktivist groups that target countries like Israel, the United States, and India, long before the war broke out. These groups are usually from Indonesia, with participation from different Islamic countries such as Malaysia, Pakistan, Bangladesh, Iraq, Morocco, and Iran.
What has changed since the war is the noticeable increase in the number of these groups and radical Islamic users, who collaborate to target Israeli entities, particularly in cyberspace. Their tactics include a range of actions, such as hacking into Israeli websites, employing DDoS attacks to disable them, executing website defacements, and even gaining control of applications and IoTs used by Israelis.
The main targets of these cyberattacks are the websites, servers, and other platforms associated with government, municipal, and infrastructure organizations, as well as healthcare institutions such as hospitals and healthcare organizations.
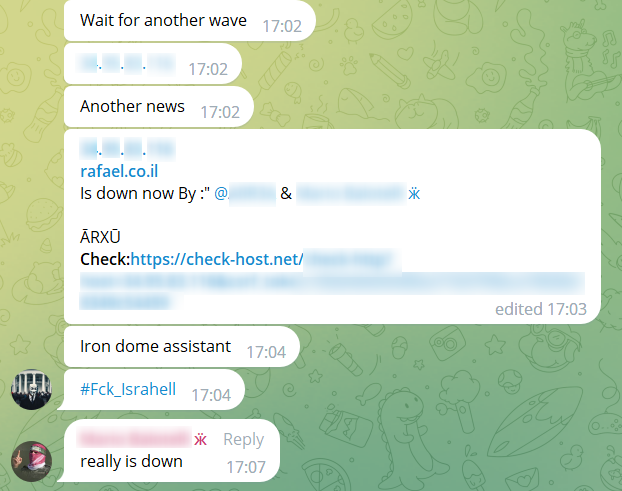
However, the Israeli private sector isn’t immune to these attacks. This can be seen in the following post taken from Telegram calling for a DDoS attack against an Israeli cyber team. The post is written in Malay and reads: “Assalamu Alaikum and greetings of liberation. This is our general target tonight. My advice to those of you who use VPN – please use a VPN of a different country! We storm this website until it’s down! Takbir!”

As for their operation in the deep and dark web networks, we see that almost all of these cyber criminals and hacktivists maintain accounts on Telegram. The cybercriminal groups, about 80 in total, in particular also operate channels and closed groups, where they announce attacks they have carried out and upcoming attacks, share sensitive information they compromised by hacking attacks, and even conduct real-time attacks.
Some hacktivist groups that want to gain reputation and recognition also operate outside encrypted chat applications like Telegram and run accounts on popular open social networks such as Twitter, TikTok, and YouTube.
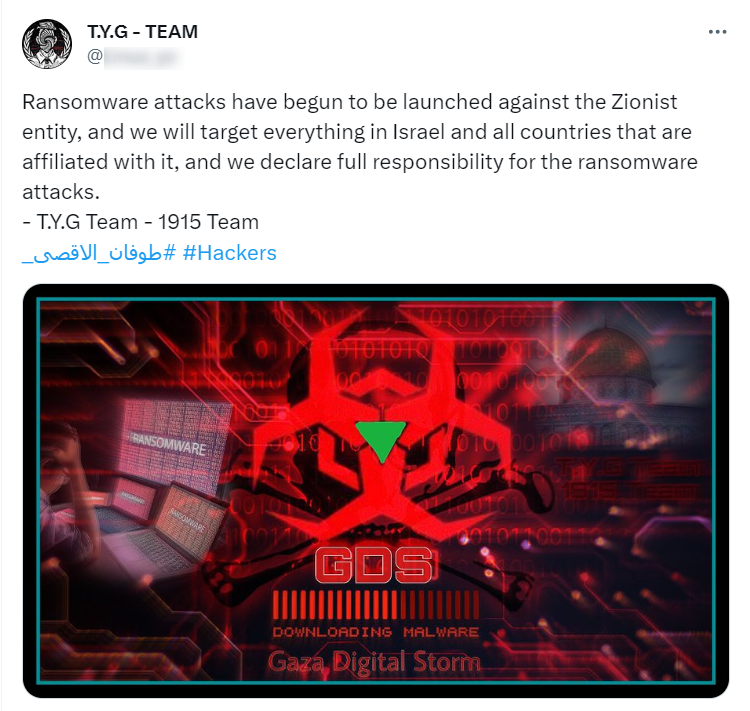
Some cybercriminals exploit the situation for personal gain or are driven by specific agendas and engage in the publication or trade of compromised data belonging to Israeli entities. This data can include previously disclosed information that has been reposted or newly acquired data obtained during ongoing cyberattacks. It often comprises sensitive details related to both private and public companies, as well as Israeli citizens. This data gains particular traction and may be utilized by other cybercriminals in future attacks.
The distribution and documentation of stolen accounts and sensitive information can also be used as part of psychological warfare aimed at intimidating the Israeli public.
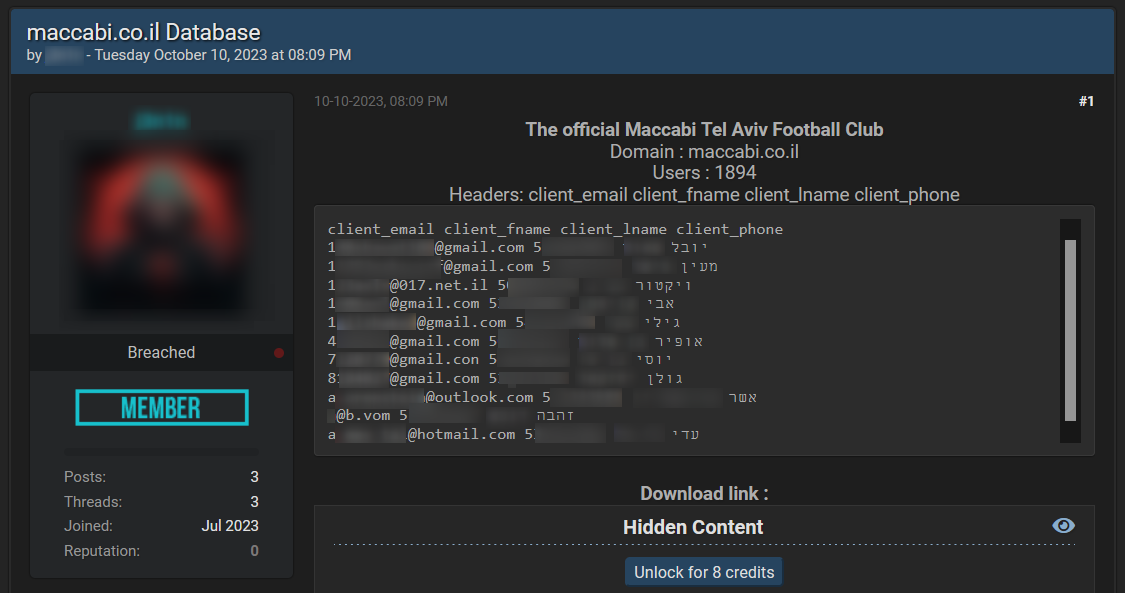
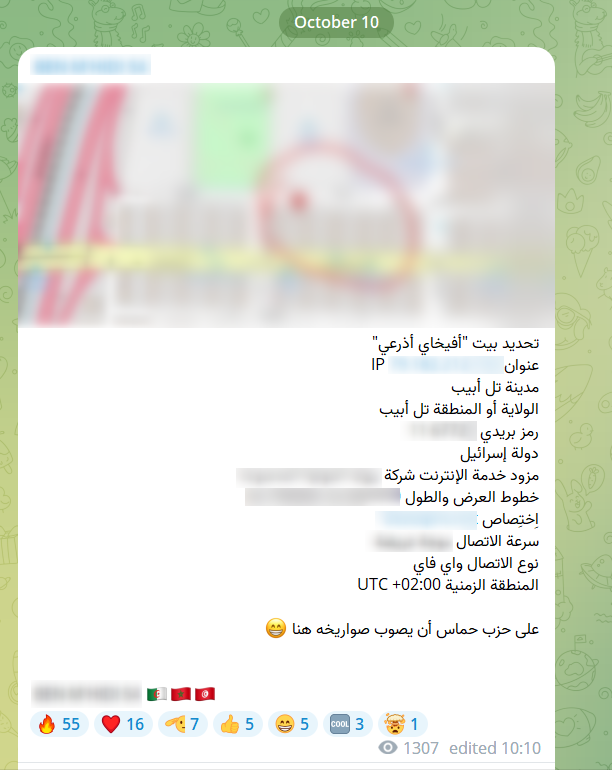
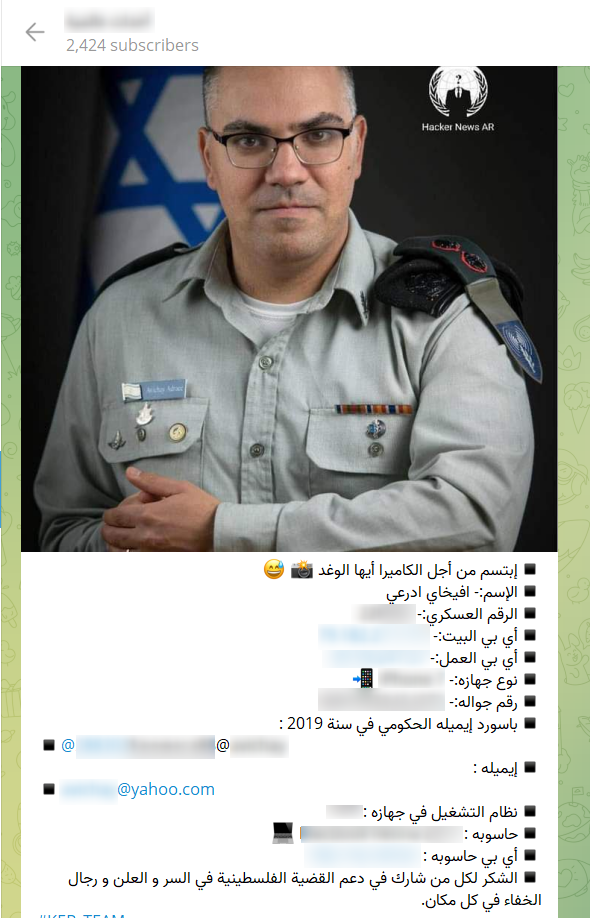
Another important risk to note within this space is instances of doxxing that target public figures in Israel, as they present a significant risk and threat.
For example, a recent post disclosed sensitive information, such as the IP address and residential details of IDF spokesman in Arabic, Avichay Adraee:
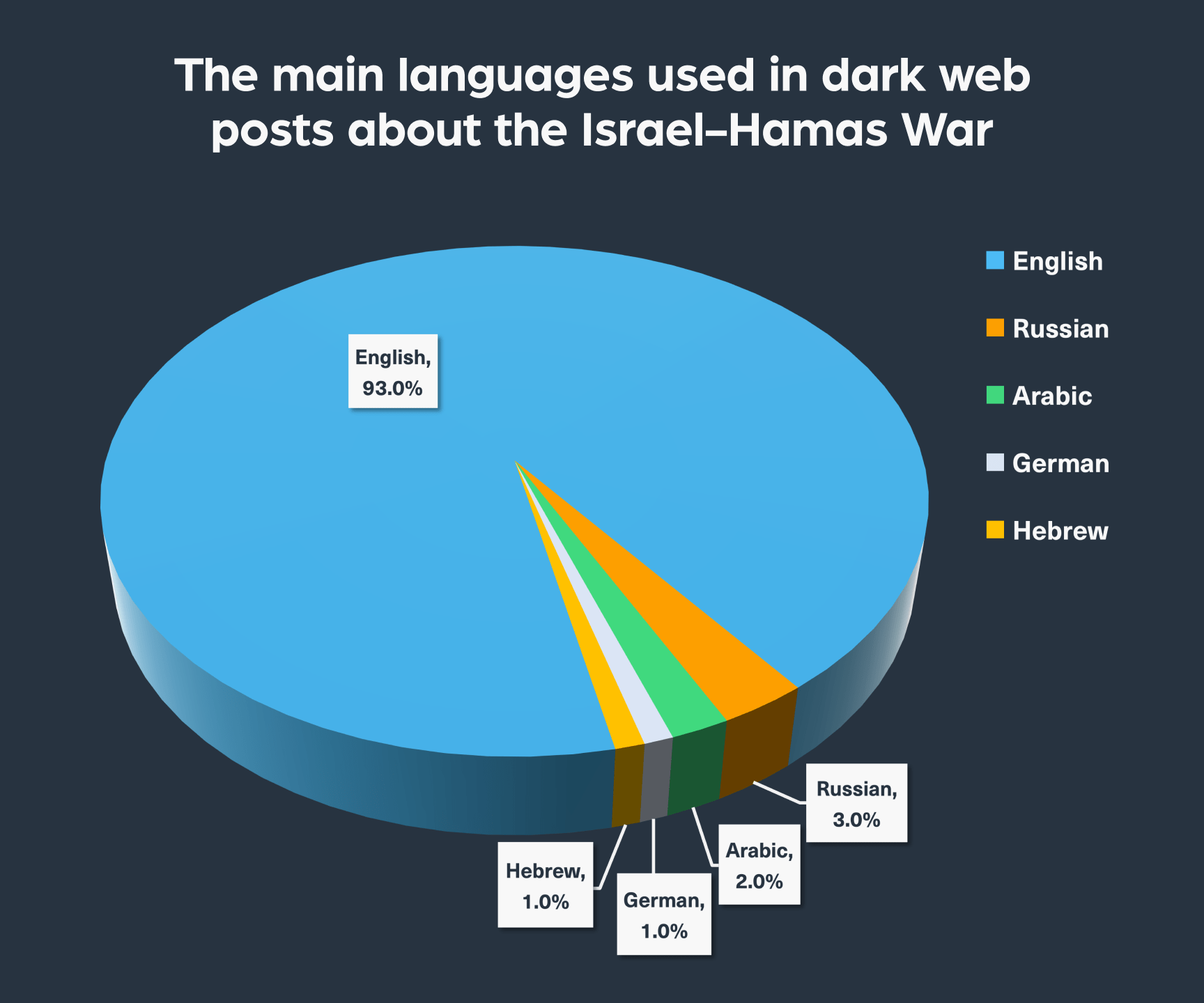
After examining the conversations in the cyber realm, we’d like to take a quick bird’s-eye view as to where the chatter is coming from. We ran a search to discover the languages used in relevant content. The discussions show how widely discussed the conflict is around the world, with English emerging as the most used language, followed by Russian, Arabic, German, and Hebrew.
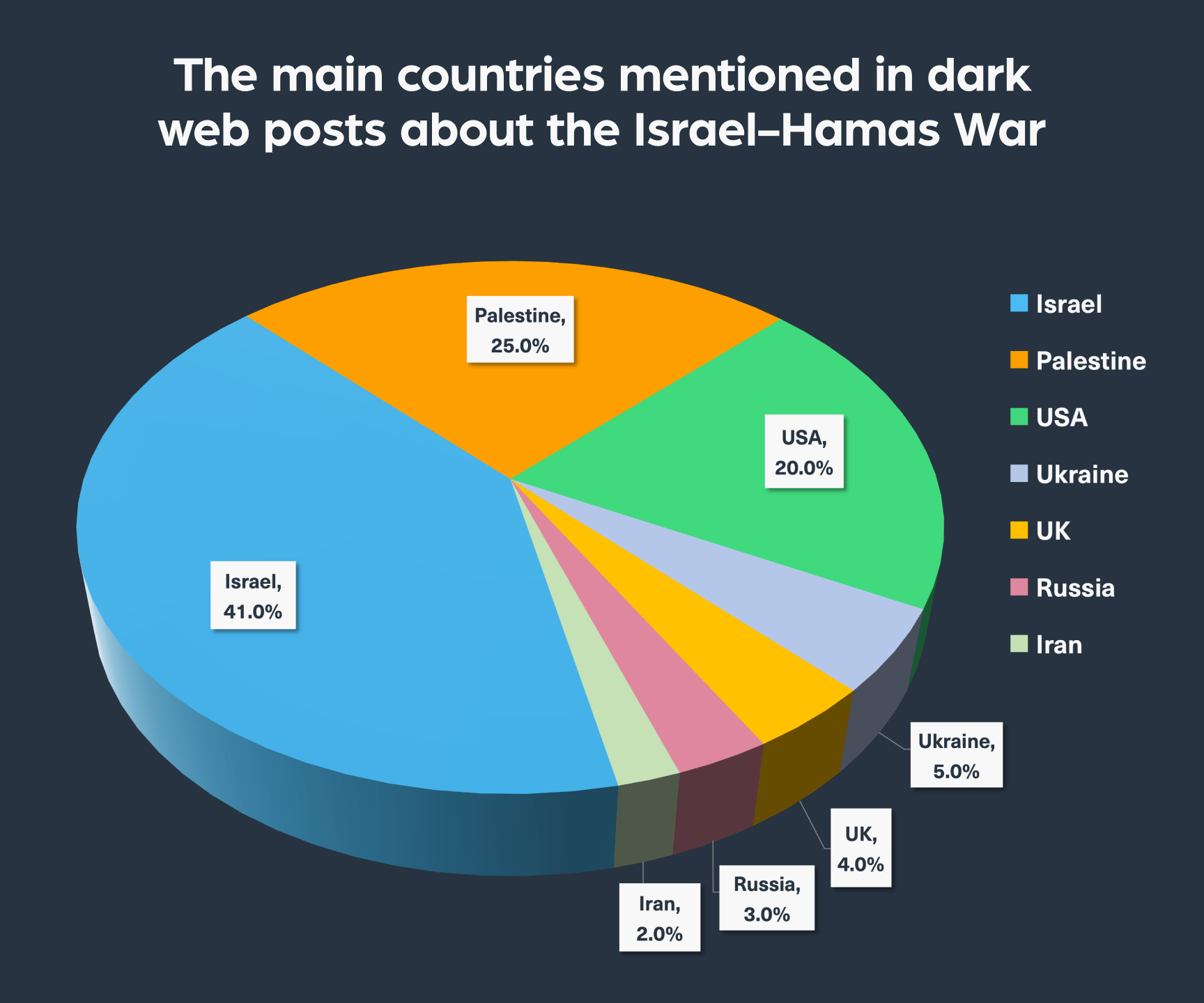
We also searched for mentions of locations in the text to gain some deeper context. Here, in addition to the obvious mentions of Israel, Palestine, and Gaza, we also found mentions of other countries such as the United States, Ukraine (seemingly used as a point of comparison to the situation in Israel), UK, Russia, and Iran.
The deep and dark web is increasingly being used as another space of conflict in times of geopolitical tensions and war. A notable example of this was when the Russia and Ukraine war broke out, which we covered in length in the past. Events of this nature, particularly those attracting international media attention, find significant traction on these hidden networks. Because they are used as another layer in today’s modern warfare, whether by launching attacks against the infrastructure of a country involved in the conflict or by fueling psychological warfare, monitoring these spaces is instrumental in protecting public and private bodies in times of war.

Do you use Python? If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API.

Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data.

A quick guide for developers to automate mergers and acquisitions reports with Python and AI. Learn to fetch data, analyze content, and generate reports automatically.