How to Automate Supply Chain Risk Reports: A Guide for Developers
Do you use Python? If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API.

Operating beyond the reach of traditional search engines, the dark web is a clandestine internet realm – infamous as a hub of illicit activity. Although the dark web itself is not inherently malicious, its anonymous nature has earned it a justifiable reputation as a home for cybercrime, illegal markets, hackers, and hacking tools and services. This makes the dark web a legitimate and pressing concern for government agencies and business organizations alike.
For businesses, the dark web is a haven for trade in stolen data, trade secrets, and proprietary information – an activity that places organizations at risk of reputational damage, financial losses, and legal or regulatory liability. Government agencies can face national security risks owing to dark web activity, notably espionage and the distribution of classified information.
Advanced dark web monitoring tools offer organizations better awareness of the myriad threats lurking in the dark web – threats can range from just annoying to actually existential in their severity. This knowledge enables the implementation of more robust, more targeted, and more cost-effective cybersecurity measures.
Dark web monitoring is crucial to proactively address and mitigate a wide range of threats – threats that organizations really need to know about. For example, the sale of proprietary data from industrial espionage, human resources PII exfiltrated by a disgruntled employee, or the fact that threat actors are targeting specific organizational assets or a vulnerable component of the supply chain. Whatever the threats, by understanding their exact nature as they emerge, organizations can better head them off before they reach fruition and impact business goals or even business continuity.
What are the most common types of threats facing organizations that dark web monitoring can alleviate?
Unauthorized individuals who gain entry into organizational systems can easily exfiltrate confidential information. Such data can then be bought and sold on the dark web for the purposes of further attacking the organization (by exploiting specific CVEs, for example), stealing identities, or orchestrating a DDoS attack. Dark web monitoring is a valuable way to identify the initial signs of a data breach, granting organizations the precious time required for a proactive response.
The exposure of confidential organizational data can carry severe repercussions to an organization’s reputation, can lead to civil legal actions against the organization on the part of injured parties, and can even carry criminal liability. In the case of government agencies, consequences can be especially dire – potentially jeopardizing lives. Dark web monitoring can mitigate the risk of private data ending up in the wrong hands by quickly identifying and addressing previously unknown breaches that resulted in data leaks.
Malware and phishing attacks are employed by threat actors to obtain access to confidential information. Dark web monitoring plays a crucial role in mitigating the impact of such attacks – helping organizations identify potential threats early by actively scanning the dark web for signs of malicious activity and the sale of stolen data. A proactive approach towards such threats allows for timelier responses – strengthening cybersecurity measures, alerting employees to phishing attempts, blocking malicious websites, etc.
Through the dissemination of false information or the fabrication of counterfeit accounts, cybercriminals can use the dark web as a platform to assault an organization’s reputation and brand, which can translate into business losses or even a threat to business continuity. Such attacks can target both organizations and their supply chains or partners. By leveraging dark web monitoring, organizations can proactively search for threats to their brand, averting potential damage before it garners mindshare or public attention.
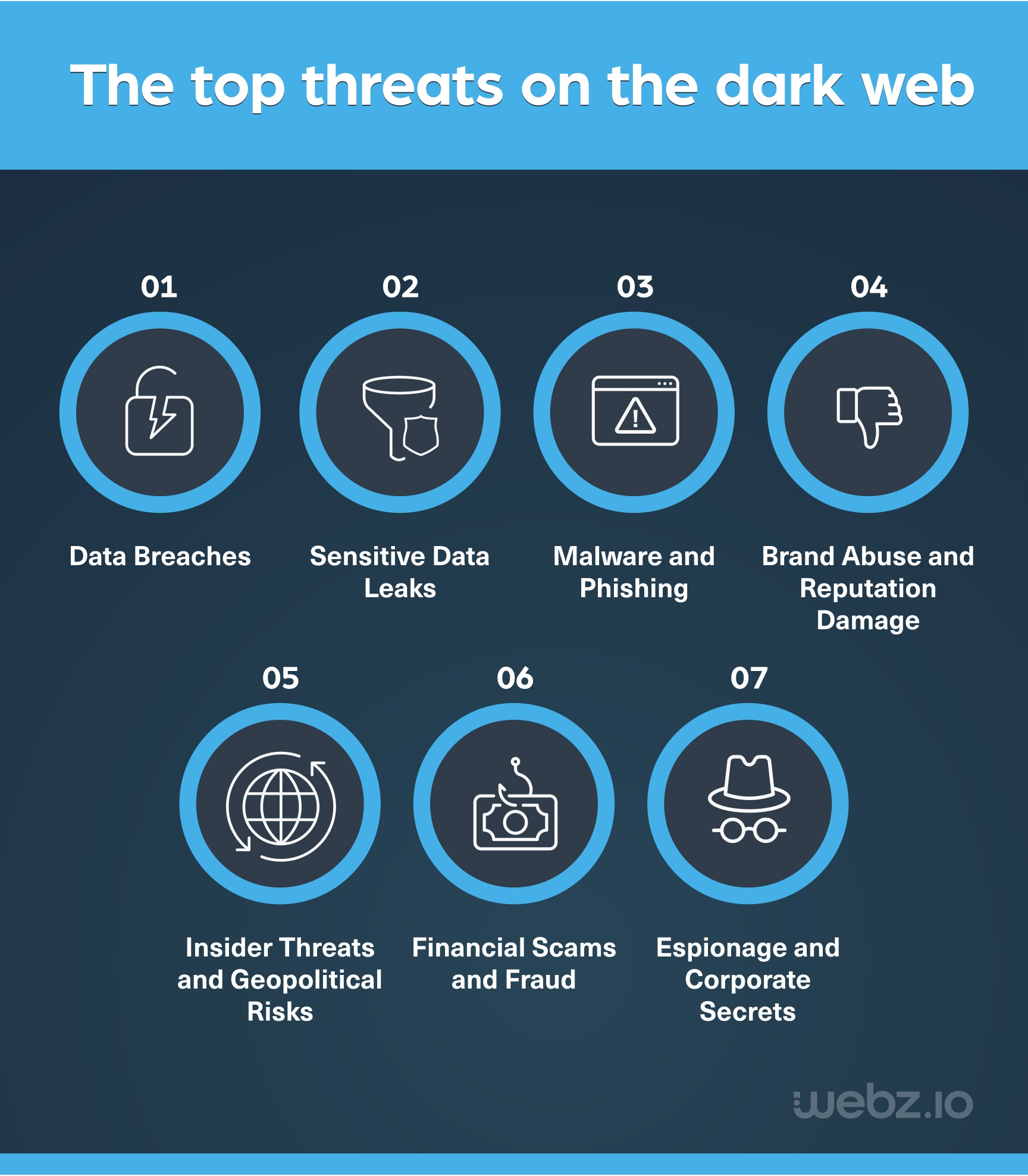
Employees can illicitly disclose sensitive data on the dark web – sometimes for personal gain, and sometimes for revenge against perceived mistreatment. When this happens within government entities, what are inherently internal threats can escalate into a geopolitical crisis – potentially provoking intervention by foreign agents or fomenting state-sponsored cyberattacks. Through vigilant and ongoing monitoring of the dark web, organizations can detect insider threats and take proactive measures to mitigate their substantial risks.
By continuously scanning hidden online marketplaces and forums to identify stolen financial data, compromised accounts, or discussions related to fraud, dark web monitoring can mitigate the impacts of financial scams and fraud. Early detection allows organizations to take faster action like alerting affected individuals, securing compromised accounts, and reporting illegal activities to authorities. This shrinks the window of opportunity for scammers and fraudsters – minimizing both financial losses and reputational damage.
Dark web monitoring mitigates the risks of espionage and corporate secrets leaks by tracking clandestine communication channels and identifying discussions or transactions related to such activities. By catching espionage early on, organizations can quickly initiate countermeasures like shoring up cybersecurity, taking legal actions, or adjusting security protocols. Dark web monitoring is a critical early warning system, allowing organizations to better protect their sensitive assets.
Dark web monitoring helps organizations detect and mitigate a wide scope of threats – from data breaches and leaks to malware and phishing attacks, including financial scams and corporate espionage. By using dark web monitoring platforms and services effectively, organizations can proactively identify and address threats like these – safeguarding their data, reputation, and stability.
There are many types of tools and platforms that facilitate monitoring of the dark web.
Data analytics solutions leverage advanced machine learning and AI to quickly identify patterns and detect potentially malicious activity in dark web data. Third-party threat intelligence feeds like VirusTotal and BitDefender update about malicious activities in real-time, which aids in the detection and mitigation of emerging threats. Professional dark web monitoring tools, like those offered by webz.io, cater to organizations that may lack the resources or infrastructure for in-house monitoring.
Additionally, threat intelligence platforms gather and analyze critical threat data from numerous dark web sources, then deliver actionable insights to mitigate dark web threats. Cyber knowledge bases like MITRE ATT&CK and OWASP assist organizations by keeping them informed of evolving security threats. Security and vulnerability databases like the National Vulnerability Database (NVD) and Common Vulnerabilities and Exposure (CVE) database also feature extensive information on potential vulnerabilities and security risks.
Organizations have a large and diverse toolbox at their disposal to enhance their dark web monitoring capabilities – empowering them to proactively detect, mitigate, and respond to threats originating from the dark web and elsewhere.
Whereas the dark web can present substantial risks to both government agencies and businesses – effective dark web monitoring can proactively identify and mitigate these threats. Incorporating dark web monitoring into overall cybersecurity strategy empowers organizations to protect their data and reputation while responding promptly to potential threats. Choosing the right tool or platform for dark web monitoring helps organizations ensure the security not only of their digital assets but also of their core business or activity itself.
Whether you need an advanced dark web monitoring platform or dark web data to automate your own monitoring solution, Webz.io can help. Talk to one of our experts today!

Do you use Python? If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API.

Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data.

A quick guide for developers to automate mergers and acquisitions reports with Python and AI. Learn to fetch data, analyze content, and generate reports automatically.