How to Automate Supply Chain Risk Reports: A Guide for Developers
Do you use Python? If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API.

Supply chain networks have become increasingly vulnerable. From cyberattacks to counterfeit products, organizations must proactively monitor potential threats to safeguard their supply chains and their bottom line.
Supply chain attacks are not new. The famous Target breach that took place in late 2013 was a supply chain breach. The threat actors gained access to Target by using credentials stolen from its HVAC provider, Fazio Mechanical Services. Since then, we’ve seen a flow of hundreds of supply chain attacks targeting different industries, from pharma to energy, finance, and more.
Although incidents like SolarWinds have played a significant role in fueling this awareness, it is only in the past few years that we have all recognized the huge impact of these risks. According to SecurityWeek, in the last 3 years supply chain attacks increased by 742%.
While there are various solutions that are used to detect and mitigate these attacks, one emerging solution has gained more attention: dark web monitoring tools. These tools enable companies to proactively identify and address supply chain risks originating from the deep web and darknets, where illicit activities often take place.
In this post, we will explore how dark web monitoring tools can enhance supply chain risk management and explore how easy it is to monitor such risks in the dark web, by using Lunar, Webz.io’s new dark web monitoring tool.
The process of monitoring supply chain risks can be done by using two models:
The analyst should list TTPs that match the vendors of the target company or vendors who have integration or shared resources with the target company. Once a vendor risk, like phishing, malware, or social engineering, is found, it should be evaluated and reported with recommendations to mitigate possible threats.
A Third-Party Risk Management (TPRM) analyzes and minimizes risks associated with outsourcing to third-party vendors or service providers. This could mean, for example, detecting a recent exploit mentioned in the dark web that can be associated with Microsoft as a supply chain risk. Effective supply chain monitoring tools help identify these risks by searching for vendor exploits and vulnerabilities across dark web sources.
Let’s take a look at an example to illustrate how we can perform third-party risk monitoring on the dark web.
The need: The cyber analyst needs to protect Ford Motors. One of the company’s vendors is Fortinet, which provides IT & cyber security services. The software it provides includes FortiGate firewalls, FortiEDR endpoint security software, and FortiSandbox sandboxing software. This means that the analyst will look for Fortinet software vulnerabilities on the dark web as they could pose a risk to Ford Motors as a result.
To illustrate the flow, we’ll use our dark web monitoring tool, Lunar.
The starting point would be to run a very general query, such as (fortinet OR fortigate) on Lunar.
As you can see below, Lunar returned many mentions (27000+), which means we’ll need to narrow it down to a management size of relevant results.
In order to trim the long list down to relevant results related to Fortinet, we can use several powerful filters, including:
Even after using them, we get too many results, so we can narrow them down by using the timeline to select recent results, which narrows the list down to 1010 documents.
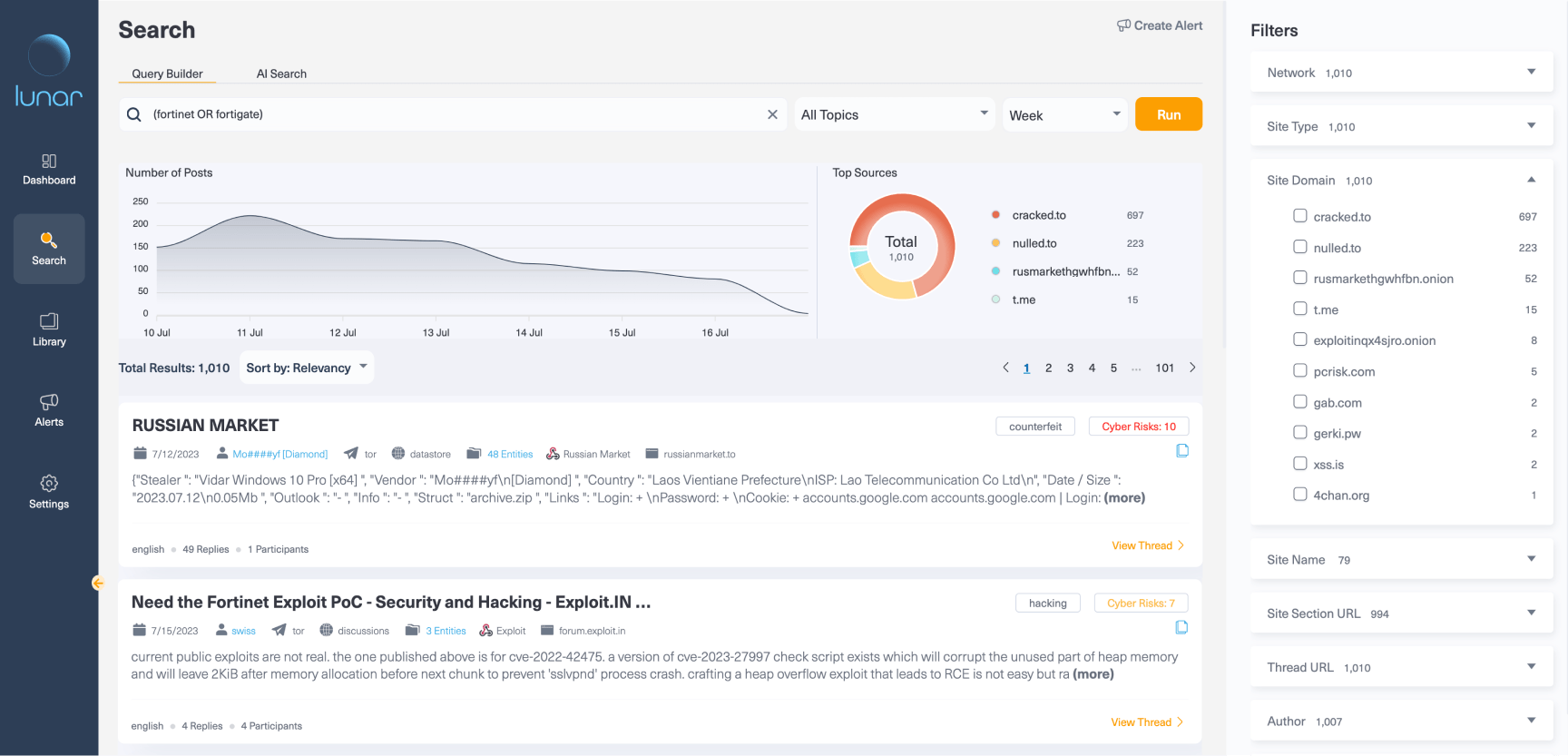
Since 1000+ results are still a big number to analyze, we can narrow it further down by using the CVE filter to find registered vulnerabilities.
This helps us shrink the list from 1010 results to only 15 documents where threat actors mentioned CVEs. The most mentioned one, CVE-2023-27997, appears at the top of the list.
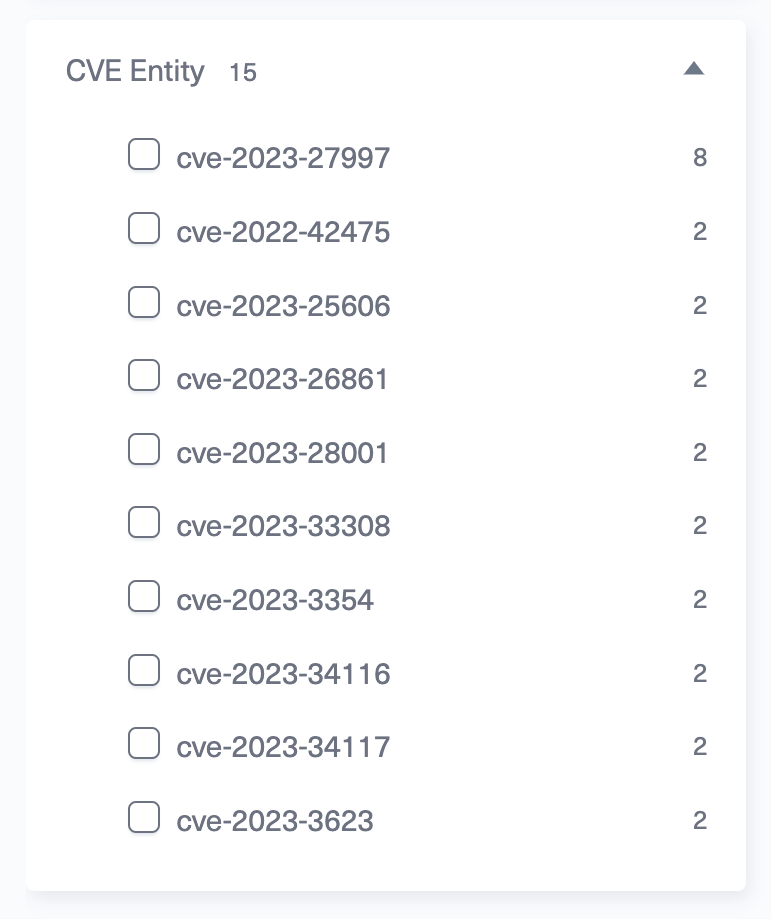
CVE-2023-27997 is a heap-based buffer overflow vulnerability [CWE-122] in FortiOS version that allows unauthenticated access to Fortinet device (RCE). This means that the severity of this vulnerability is critical and it must be reported with a patch and a mitigation plan to all relevant Fortinet products that Ford Motors is using.
Clicking the CVE dynamic filter and then choosing the specific value CVE-2023-27997 will narrow down the results to eight.
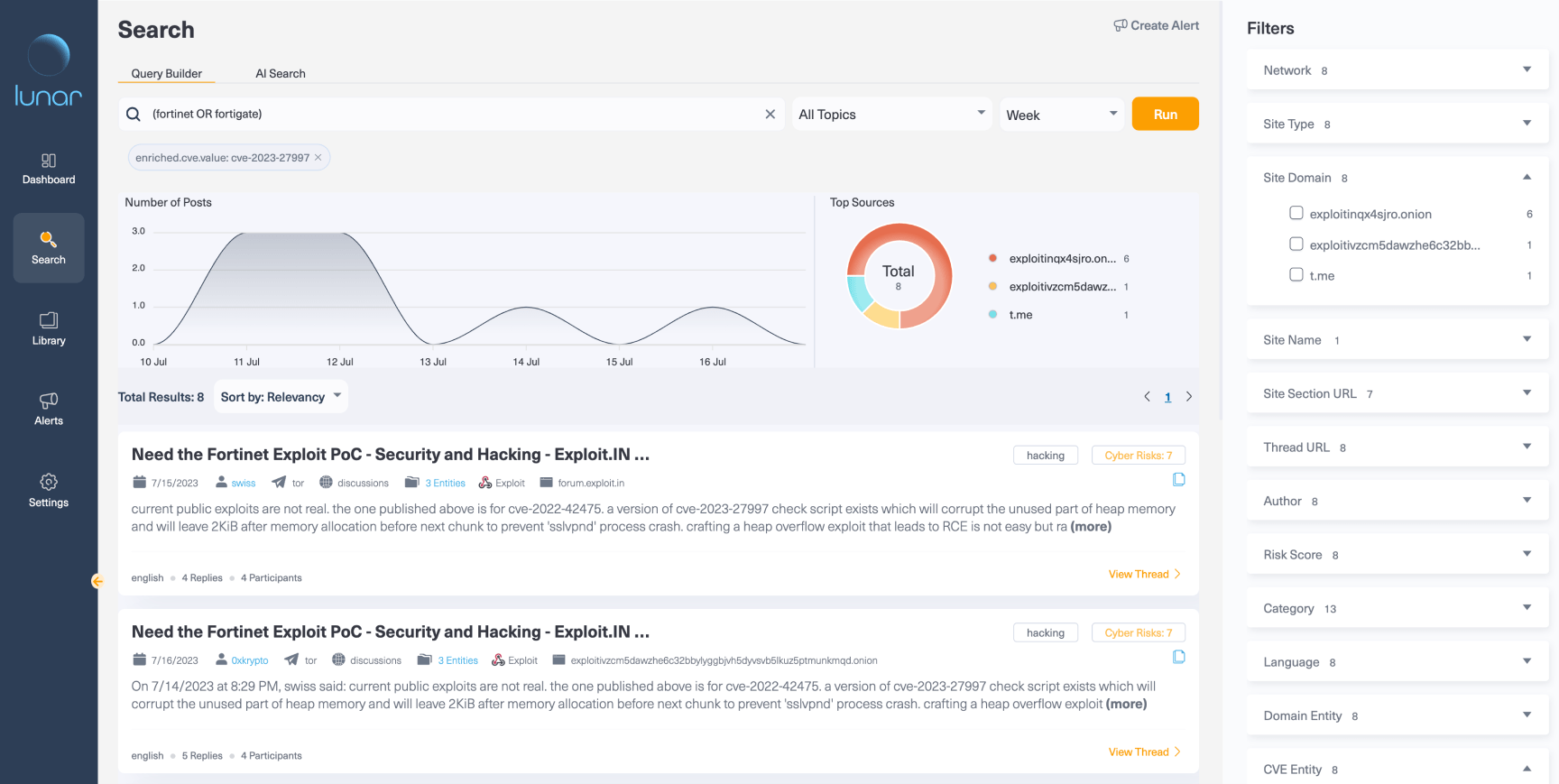
Looking back at the results, we managed to narrow down to eight documents. Seven out of eight are from Exploit, all from the last few days. The CVE was published on June 20, three weeks earlier.
We then can continue the TPRM process and refine the evaluation by:
After going through these different steps, it’s possible to compile actionable steps to mitigate these risks.
Dark web monitoring tools, like Lunar, can help monitor supply chain risks in a number of ways, including:
With dark web supply chain threats continuously on the rise, dark web monitoring tools play a key role in protecting against emerging threats and mitigating ongoing risks. The job of a TPRM is hard and monitoring these hidden spaces on the web is an endless task that requires simple solutions. For that reason, we have worked with cyber analysts to develop a tool to help them monitor and investigate threats on the dark web with ease.
The dark web is where threat actors gather to buy and sell exploits, stolen credentials, and vulnerabilities targeting your suppliers. They discuss supply chain attack methods, share tools, and coordinate campaigns against vendors. Monitoring these spaces reveals threats before they reach your organization’s supply chain or impact your vendors’ operations.
Dark web monitoring tools search for your vendor names, products, and services across forums and markets. You get alerts when exploits or vulnerabilities mentioning your suppliers surface. This gives you time to contact vendors, discuss patches, and put mitigation strategies in place.
Vendors face credential theft, unpatched software vulnerabilities, malware distribution, and ransomware targeting. Threat actors exploit weak security in smaller suppliers to gain access to larger organizations. A single vulnerable vendor can compromise multiple companies through supply chain web attacks, amplifying risk across interconnected networks.
Yes. Small businesses face supply chain risks just like enterprises do. Dark web supply chain threats targeting vendors affect organizations of all sizes. Dark web monitoring tools help teams of any size track their vendor ecosystem without adding security headcount or expensive infrastructure.
Lunar provides intuitive filtering and risk scoring designed specifically for supply chain monitoring. You narrow results using CVE filters, risk scores, and timelines to find actionable intelligence quickly. The platform combines dark web data with structured analysis to help analysts identify and prioritize threats faster than manual searching.

Do you use Python? If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API.

Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data.

A quick guide for developers to automate mergers and acquisitions reports with Python and AI. Learn to fetch data, analyze content, and generate reports automatically.