How to Automate Supply Chain Risk Reports: A Guide for Developers
Do you use Python? If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API.
Throughout history, monitoring illegal and criminal activities has evolved. In the past, investigating and identifying criminals used to involve various physical measures, such as physical surveillance and later – phone tapping. But in today’s digital world, where a big part of criminal activity has transitioned from the physical world to the cyberspace, tracking threat actors also involves gathering intelligence in the deep and dark web.
Defending against such threats requires prior good knowledge of threat actors who pose a risk. By monitoring their activities and chatter, you can gain insight into:
Based on this intel, law enforcement agencies and cybersecurity companies can start profiling threat actors in the deep and dark web.
There are various investigations that can be performed when using structured data from the deep and dark web.
Let’s take an example of a threat actor called “Sedy” and walk through the steps you can take with dark web monitoring to kickstart your threat actor profiling.
Monitoring the activity of threat actors on the dark web helps identify early indications of threats and find key leads for further investigations. We use various techniques to do that, including phrases associated with illegal activities.
The result of this search found a post by a threat actor under the name Sedy on the hacker forums Raidforums. In the post, Sedy mentioned he has a hacking group for hire.
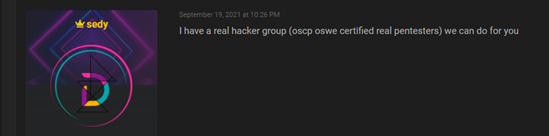
Using an advanced query, we were able to retrieve over 100 posts written by Sedy over the past two years. The posts were written on 7 different hacker forums. The high volume of content we could find is an indication of the level of risk posed by the threat actor.
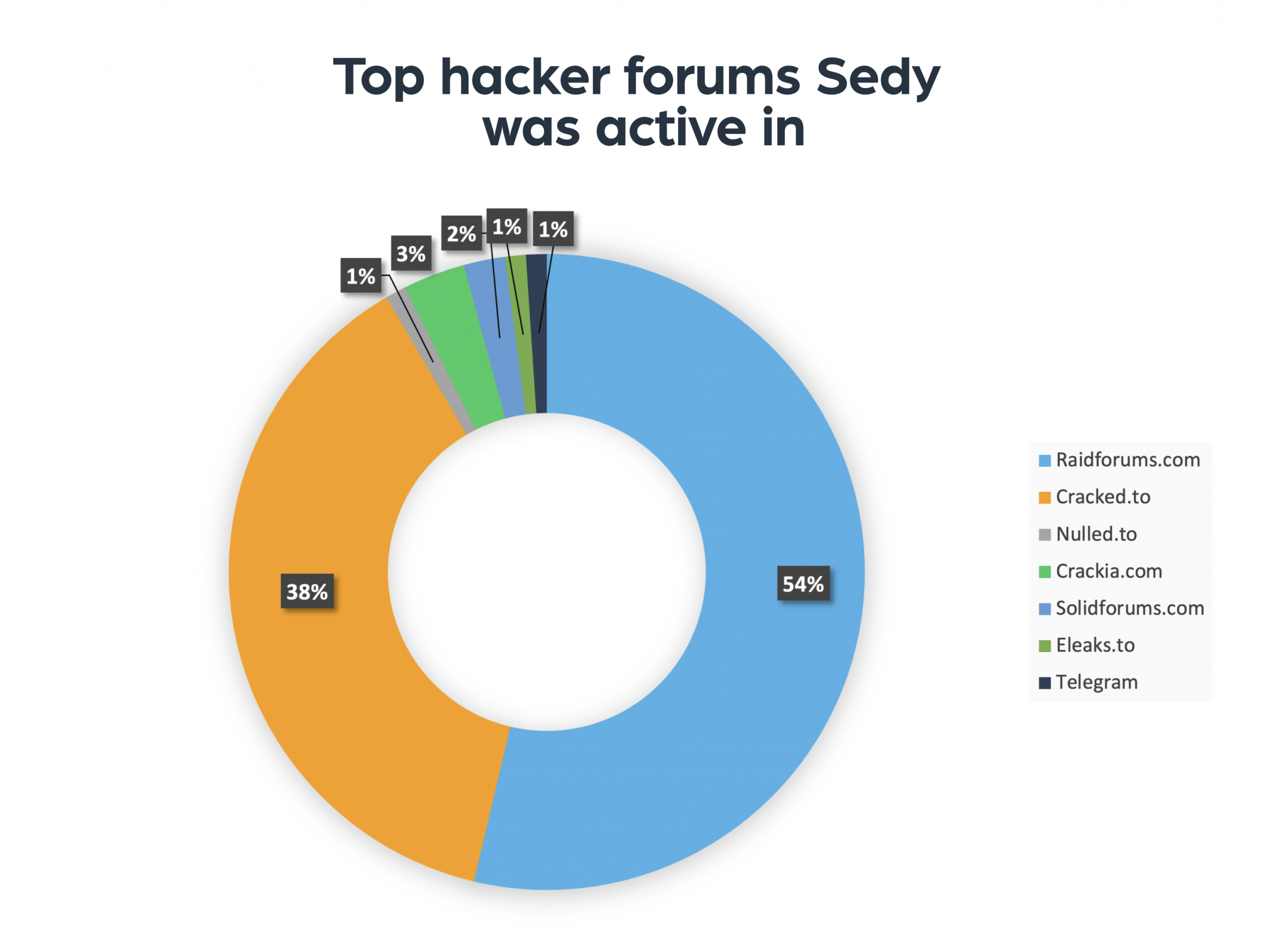
The next step is to search whether the threat actor left any contact information in any of his posts. This information can include email addresses, phone numbers, links to profiles on other sites and more. We often find posts where threat actors share a crypto address they use to receive payments for their services while protecting their anonymity.
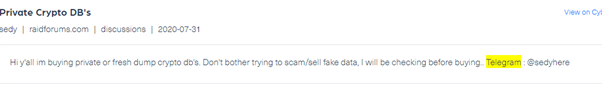
By reviewing Sedy’s posts, we can identify several contact details he left online. Here we could find the threat actor’s Instagram account, Discord account, Discord shop and Telegram account:
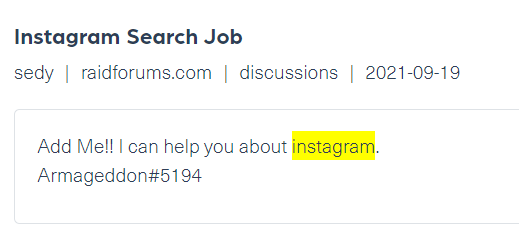
These pieces of information can be used to track the footsteps of the threat actor across the deep and dark web.
Using advanced queries, we can dive even deeper to track threat actors who use different names on different sites.
For example, we ran a query for posts that were written by Sedy using his Telegram account, which we discovered in the previous step (#3), under the name “sedyhere”:
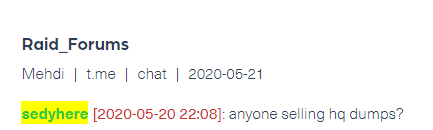
When we ran the initial query to find Sedy’s posts, we detected a post from Telegram as well, under the author: Sedy. This may indicate that this threat actor has more than one Telegram account.
In this step, we’d look for different threat actors who shared the same contact information or shared the same content on different platforms. These links can play a crucial role in any further investigation, since cyber criminals often use anonymous avatars and regularly change their names.
Running a query on Sedy’s contact information, we retrieved 4 different posts from 4 different authors that mentioned the same contact details. This could mean that Sedy has more identities on the dark web or that he has other partners in crime.
These findings provide you with a good basis to perform a deeper and comprehensive threat actor profiling.
Threat actor profiling is a long process which starts with contextualized and comprehensive data.
But where should you start?
The wider the scope, the more content you can cross-check, and run to identify cybercriminals. To find these elusive cybercriminals, you’ll need to dive deeper into the secret world of threat actors. Our customers run these investigations across millions of dark web sites, forums, marketplaces, chatting applications, alternative social media platforms, paste sites and more.

The deep and dark web are messy spaces with a lot of spam and clutter. For an effective and quality investigation, make sure you use structured and enriched data feeds that will enable you to run advanced queries and retrieve noise-free, contextualized and accurate results.
One thing is for certain; With cybercriminals increasingly using the deep and dark web for illegal trade and illicit activities, the use of deep and dark web feeds becomes key to tracking the activity of threat actors online.

Do you use Python? If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API.

Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data.

A quick guide for developers to automate mergers and acquisitions reports with Python and AI. Learn to fetch data, analyze content, and generate reports automatically.