How to Automate Supply Chain Risk Reports: A Guide for Developers
Do you use Python? If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API.
When two mass shooting attacks happened within hours of one another in the US last month, few might have guessed that a network of relatively unknown internet forums could have provided the common inspiration for both attackers to carry out their crimes.
The El Paso and Dayton shootings, although shocking, were both merely a symptom of the growing problem of transnational right-wing extremism. It’s a problem which straddles borders and political ideology. And a minority of its adherents are taking to internet forums, bulletin sites, and message boards to find like-minded individuals and coordinate attacks.
Two such imageboards are 4chan and 8chan (also known as infinitychan) which share a similar-sounding name but are, in fact, not related. They are, however, both well-known breeding grounds for radicalism and extremism. In 8chan’s case, given that it is still accessible through the “open web”, it can be regarded as something of an anomaly among extremist websites — it is hiding in plain sight among the many less radical forums that constitute the better-known “open” internet that all users are familiar with.
Many imageboards containing extremist content, however, can only be accessed via the dark web — and achieving comprehensive coverage over these forums is key to enabling law enforcement agencies to detect malevolent actors before they act on their plans.
Webz.io has developed a Cyber API for darkweb monitoring that is solely focused on returning results from the so-called dark web. To understand the value of a structured data stream that captures dark web imageboards, it’s helpful to understand the technical complications that surround trying to capture content shared over these channels.
Firstly, the dark web consists of a series of websites accessible only over a special browser called TOR (an acronym for “The Onion Router”). TOR uses a system called “onion routing” which allows both users and webmasters to obscure their true identities by passing traffic through a series of intermediary servers selected at random. This makes it possible for those operating hate forums, such as 4chan, to host their services without fear of their identity being compromised in the process.
To make cybercriminals’ jobs even easier, many imageboards also allow users to post anonymously, without supplying any personally identifiable information during the signup process. Given the fact that they can also rest assured that the technical setup of the network makes it difficult to trace their identity and physical location, it’s easy to understand why dark web imageboards remain attractive outlets for those looking to safely spew online racial hate.
Finally, the dark web is deliberately difficult to index. No search engine like Google exists to help users find its content or the closed clusters of communities it contains. As servers and websites constantly shift location to avoid being compromised, the job of keeping track of all the imageboards and other forums it hosts becomes extremely difficult.
The dark web is believed to be heavily monitored by intelligence and law enforcement agencies who often subvertly operate exit nodes in an attempt to trace the traffic back to its origin. As the entire system the dark web is built upon was designed to anonymize its users, the dark web has become synonymous with illicit online activity — and a sizeable proportion of it consists of just that.
It’s not all fun and games for online haters, however. With the Webz.io Cyber API, there’s a lot that law enforcement agencies can do to attempt to stay one step ahead of those posting there.
With all that in mind, how are law enforcement agencies supposed to monitor imageboards in order to catch perpetrators before they act on their possibly malevolent intentions?
Thankfully, the Webz.io Cyber API offers solutions to all of the dark web monitoring difficulties outlined above:
Since 8Chan was effectively shut down by authorities, those concerned with monitoring hate speech on imageboards need to be keeping a close eye on where those formerly active on the forum have moved to.
Webz.io’s Cyber team is continuously updating the list of websites that it indexes, but we have noted increased activity on the following forums:
ZigForum is a messaging board where users can discuss all manner of extremist-related topics.
Endchan is a dark web imageboard similar to 4chan and 8chan only accessible over the dark net by using the TOR web browser.
FacistForge is a radical, supermarcist forum involving users from different nationalities discussing topics such as the Fourth Reich and neo-Nazism.
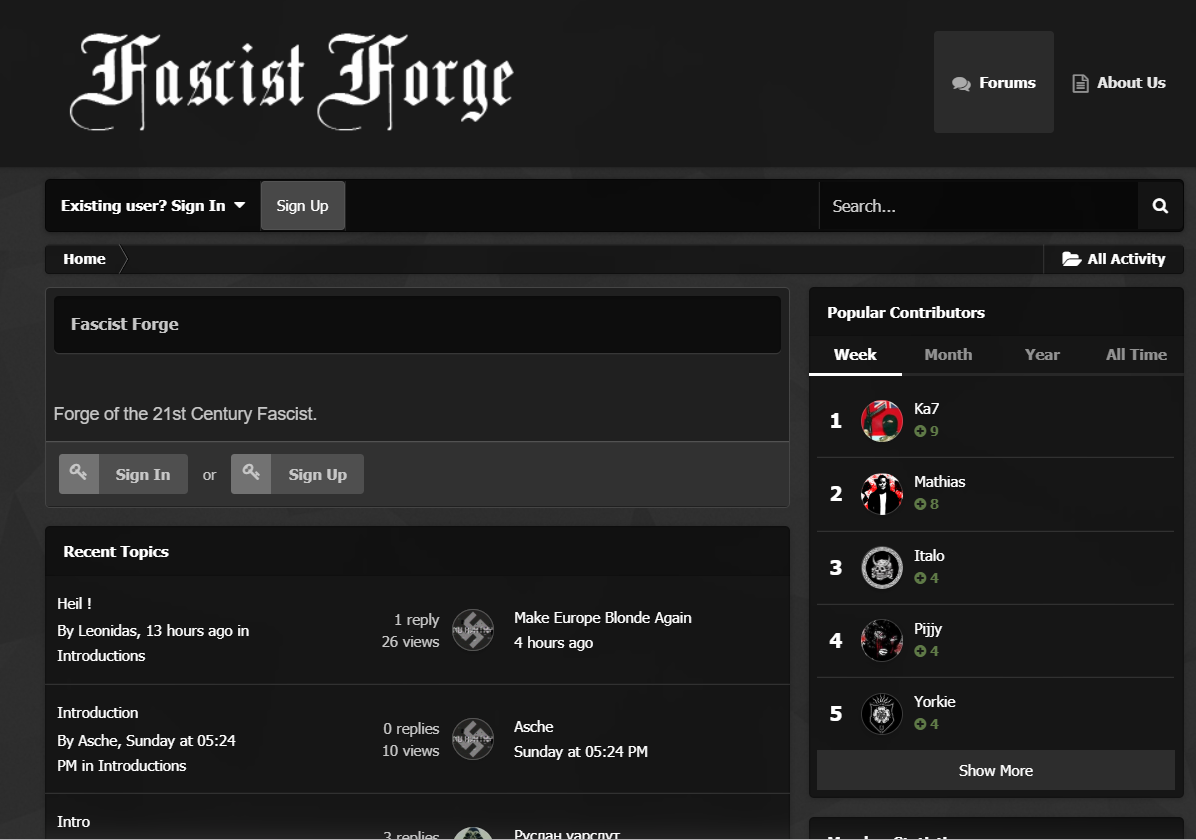
Another group of 8chan users have migrated to the website’s “bunker” on Zeronet which describes itself as the “semi-official 8chan darknet bunker”. The Zeronet mirror was set up just a few days after 8chan’s removal from both the clearnet and its .onion dark web proxy. The timely setup of the 8chan bunker on Zeronet demonstrates the difficulty law enforcement faces in keeping ahead of those operating hate forums, who can set up proxies and mirrors on new technologies just as old ones are seized or shut down. The Zeronet mirror is already in the Webz.io Cyber API.
Lulled into a false sense of security on the Zeronet mirror, many former 8chan users accidentally revealed their IP addresses which provides some clues as to where they are based.
News website The Daily Beast managed to capture 819 IP addresses for 08chan users frequenting the Zeronet bunker. It found that 437 of the IPs resolved to locations in the United States. By state, the most frequent user locations were California, Texas, Washington, and Florida.
This pie chart, extracted from Webz.io Cyber data, shows the subject matter of discussions in three leading imageboards: 8chan, 4chan, and endchan.
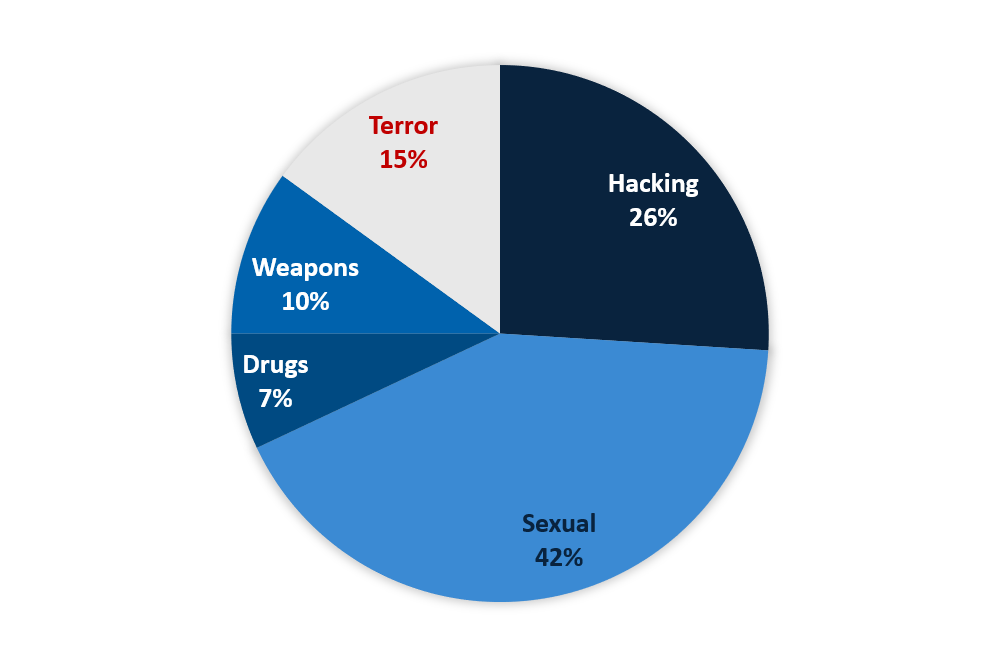
As can be seen, discussions of a sexual nature are the dominant category (42%), but terror (15%) and weapon-related (10%) threads continue to comprise a worryingly significant amount of the online activity.
In our experience monitoring imageboards including 4chan, 8chan, and others, our Cyber team has identified several trends that could be of interest to those monitoring these channels with a view to preventing terrorist activity.
Extremists often post hate dossiers known as manifestos which set out their views on a certain issue — often imputing blame for a recent political event to a certain ethnic or racial class.
Additionally, law enforcement agencies have observed that repetition across forums is a strong indicator of serious intent. Although sometimes manifestos are posted right before the attacks, as happened with the El Paso shooter, in other instances perpetrators of mass shootings and other crimes have been observed to create a frenzy of online activity, reiterating a common theme or manifesto multiple times before embarking upon an attack.
Using the Webz.io Cyber API, it’s possible to search by a specific text string, to identify cross-posts between forums, or to poll the API for a discrete entity, such as an email address or username. Doing so can reveal posts by the same user in other forums or identify associates of the same espousing the message.
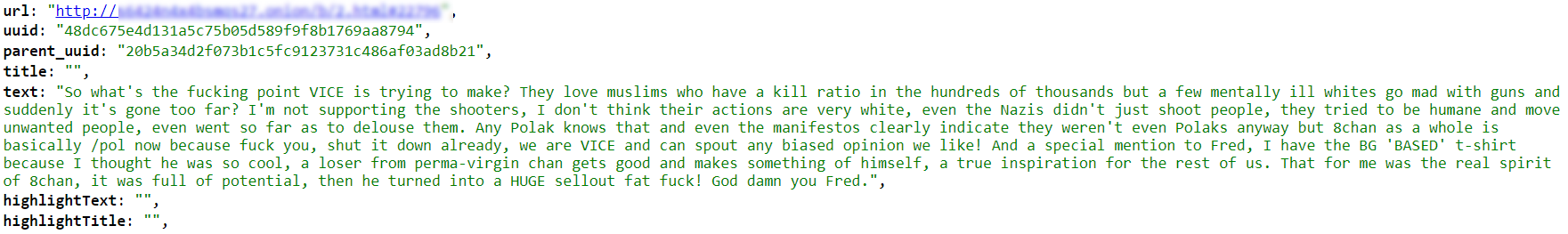
Consider the following post which was circulated by an anonymous user on 4chan inciting anti-Semitism by claiming that “the Jews” were responsible for shutting down 8chan. The original poster adds that now “they [Jews] won’t post a manifesto thread before they do it.”
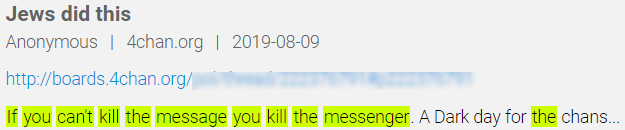

As the thread and its nested comments are all by anonymous users, we can’t begin an investigation based on a username.
However, we could build a query around the screenshot of the article that the original poster posted.
Perhaps its filename, which contains a timestamp from when it was taken from the Opera browser, will reappear exactly on other internet forums which could help us in our quest to identify the original poster.
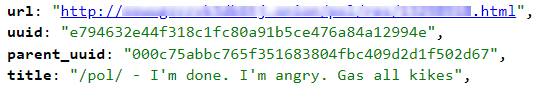
To demonstrate how we might begin another investigation into a racist poster with possible intent to act, consider this post on a dark web forum calling to “kill Jews”.
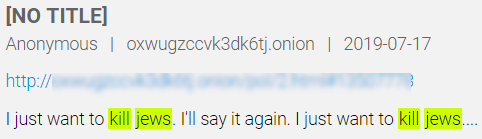
By running a simple text string lookup over the Webz.io Cyber API, we are able to find an exact match for this string on an 8chan thread. This time, there’s a username associated with the post: Jayden Sullivan. We can now query the Cyber API for this username to locate other content that this user might be posting.
The Cyber API also allows users access links to cached versions of websites whose original versions are no longer accessible online. This feature can help end-users access full-text pages of content that the API returned as meta-data but which are no longer available through their original sources.
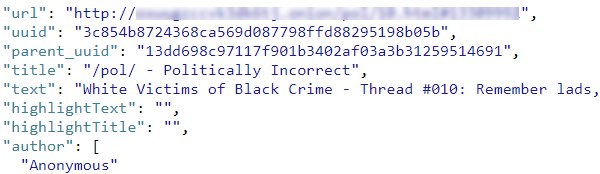
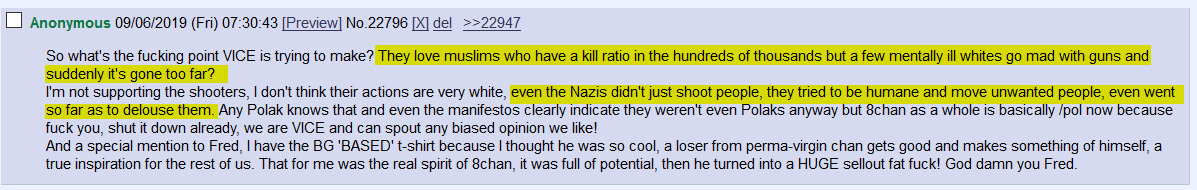
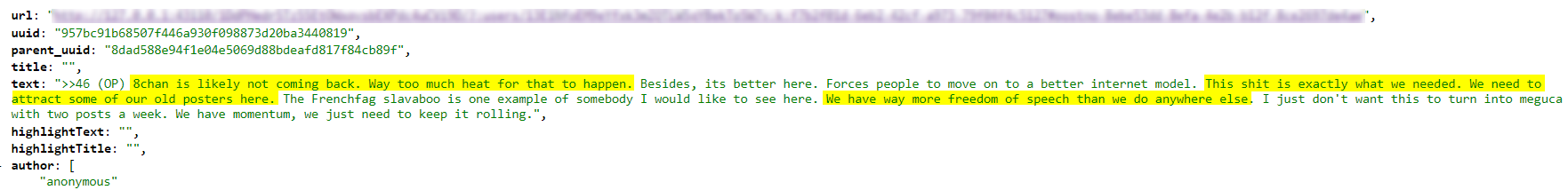
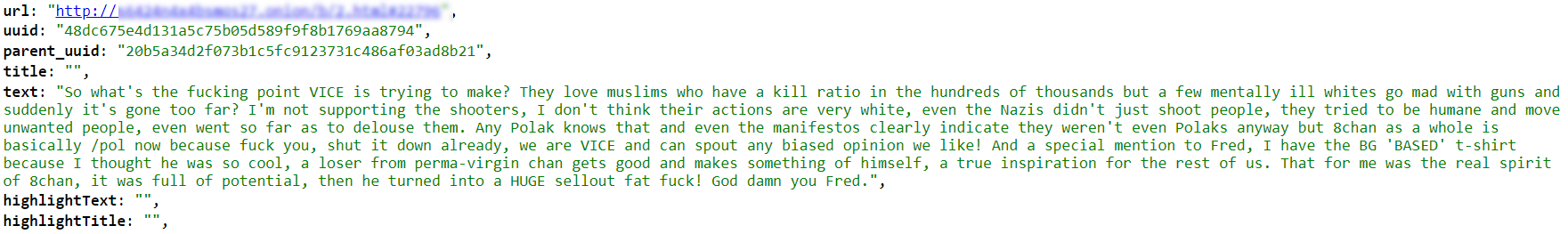
In this post captured in the Cyber API we can see an anonymous poster criticizing 8chan’s founder Frederick Brennan:
However and whenever attackers’ manifestos are posted, they often divulge specific clues that authorities could use to attempt to intervene before the attack is successful. In the case of the El Paso shooting last month, for example, the gunman, Patrick Crusius, posted a detailed four page manifesto which provided some details about the type of location he was likely to target.
His final post to 8chan, “I know that the media is going to frame me incorrectly, but y’all will know the truth. I’m probably going to die today. Keep up the good fight,” laid bare his intent to imminently commit an attack, which turned out to be the deadliest mass shooting in US history.
His manifesto, in which he stated his admiration for Brenton Tarrant, the white supremacist who carried out the Christchurch mosque shootings in New Zealnad, gave an additional clue that he was likely to target a minority community (Crusius’ intent was allegedly to target Mexicans).
Crusius even shared which weapon he had decided to use — an AK47— and, in a section advising those planning similar attacks, recommended targeting low security targets. Taken together, the hints in Crusius’ manifesto provided many keywords which could have signaled to intelligence or law enforcement agencies his intent to follow through with the attack.
High-profile individuals are frequently mentioned on dark-web forums and imageboards, particularly those that are targeted by racists and extremists solely because of their race.
The below post on 8chan, a dark web imageboard, levels a death threat against Joe Bernstein, a well-known reporter with Buzzfeed News who happens to be Jewish.
Journalists, politicians, activists, and general celebrities should be proactively monitoring any mentions of their name that appears on imageboards known to foment hatred and house discussions between extremists. Doing so is also the responsibility of law enforcement agencies who have a responsibility to safeguard the welfare of their citizens.
With the tools that Webz.io’s Cyber API offers, those responsible for enforcing law and order can gain an advantage over criminals by monitoring image boards which have often proved important vehicles for recruiting associated and planning real-life attacks.
Want to learn more about the Webz.io Cyber API? Talk to one of our Cyber experts

Do you use Python? If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API.

Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data.

A quick guide for developers to automate mergers and acquisitions reports with Python and AI. Learn to fetch data, analyze content, and generate reports automatically.