How to Automate Supply Chain Risk Reports: A Guide for Developers
Do you use Python? If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API.

Cybercriminal activity is only growing. A recent report claims that the global annual cost of cybercrime is predicted to reach $8 trillion by the end of 2023. This massive number is not only an indication that the number of cyber attacks is extending but also their sophistication.
Already over the past few years, the number of cyber attacks (especially ransomware attacks), compromised assets, and traded illicit listings has significantly increased. In this post, we’ll discuss the trends, threats, and reasons why dark web monitoring is key to protecting every business.
In the first quarter of 2023, there were an estimated 1.2 million dark web transactions related to cybercrime, with an estimated worth of $10 billion. One of the emerging trends of the past year is the use of trading platforms.
By using Webz.io’s dark web data, we have identified dozens of new marketplaces and datastores, which are mainly used for the trade of illicit goods and services, and Personal Identifiable Information (PII) that pose a real threat to corporations and individuals.
Another prominent trend that we have recently identified is the use of ransomware. Only in the first quarter of 2023, 850 new ransomware groups were observed in the dark web, based on ReliaQuest, an established cyber security agency.
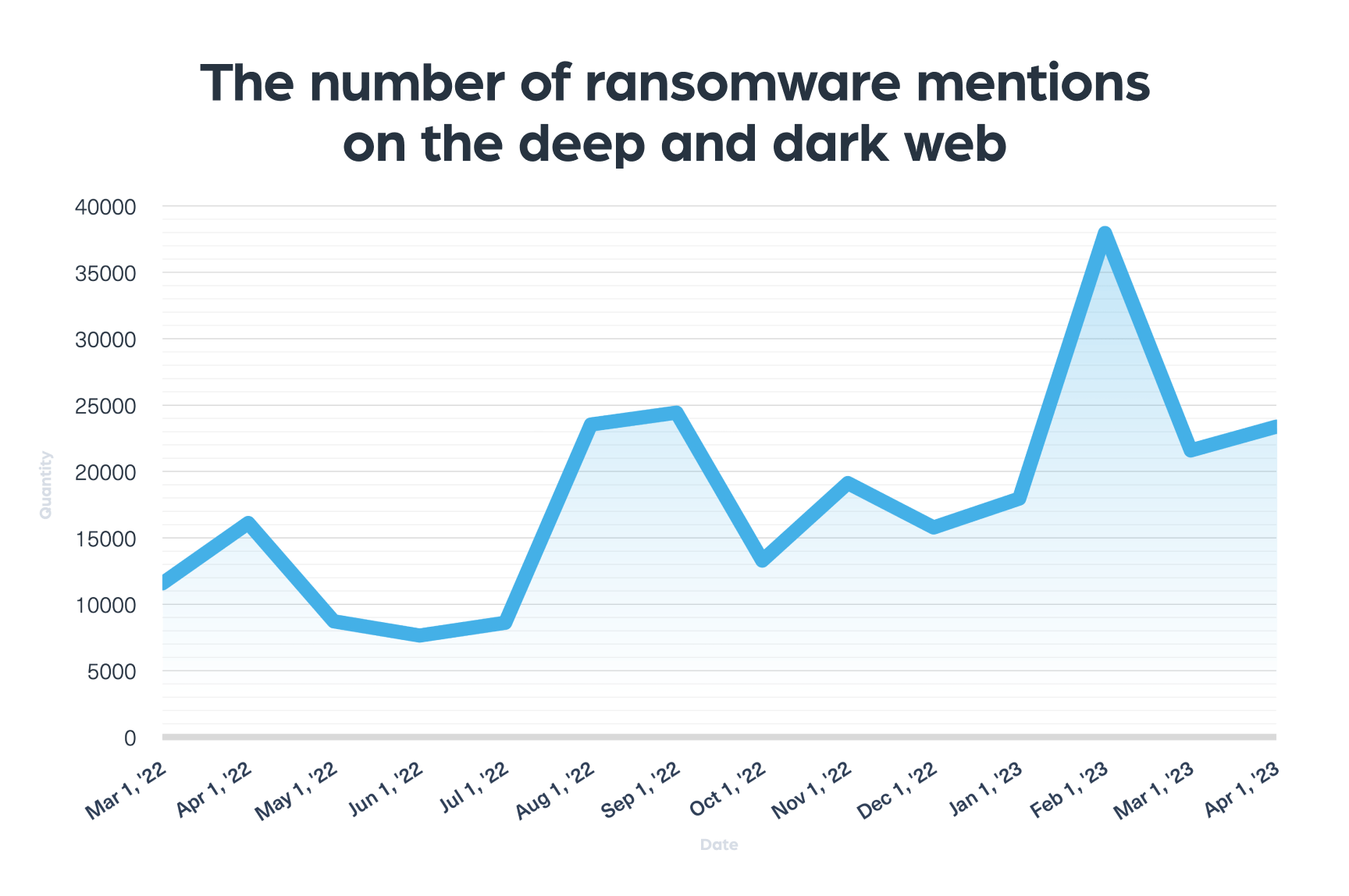
Based on Webz.io cyber data, the number of ransomware data leak sites increased by 37%. In the chart below, you can see the volume of discussions relating to ransomware on the deep and dark web from March 2022 to April 2023:
Among the illicit activities that can be found on the dark web we can find:
Monitoring the dark web is a complex and challenging task. It requires continuous collection of data from a variety of sources, including closed communities, chat apps, and marketplaces. These sources are often difficult to access, and unstable, and hacker communities try to block unwanted legitimate access.
But tracking deep and dark web sources remains top of the mind for any threat intelligence activity. Monitoring the dark web is essential for organizations that want to protect themselves from cyber threats. By monitoring the dark web, organizations can identify and respond to threats before they materialize. This can help to prevent data breaches, financial losses, and other negative consequences.
Some of the main advantages are:
Working with some of the leading companies in the world, our team of analysts has gained a deep understanding of dark web criminal activity, business needs and limitations, and the growing need and urgency to monitor the dark web better.
To easily and effectively conduct threat intelligence, every organization, and cyber analyst requires a tool that is based on the next four pillars:
In 2023, dark web monitoring plays a bigger role than ever to make every business organization more cyber-smart. Next month we’ll unveil our contribution to making dark web monitoring faster and more simple than ever before.

Do you use Python? If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API.

Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data.

A quick guide for developers to automate mergers and acquisitions reports with Python and AI. Learn to fetch data, analyze content, and generate reports automatically.